Programming the KBParadise V60 Polestar Keyboard
KBParadise V60 Polestar Keyboard
I recently purchased my first non-Model-M mechanical keyboard, the KBParadise V60 polestar.
- Night

- Day
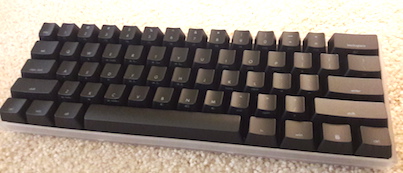
I like the 60% size, the feel of the cherry MX clear key switches, and the customization potential from its ATMEGA32u4 microcontroller. The original layout of the keyboard did not Read on →
Scala Notes Number Madness
This is another article in the scala-notes series. This one deals with what I call number madness.
What!?
Numbers are used everywhere in code, and often the type used is something like Int (Scala) or Integer/int (Java). These simple types are familiar to those of us who used languages like C but should not be used without considering
Read on →



